Workshops
Worldwide Geospatial Data Collaboration
Location Based Access Control on Geospatial Data with GeoXACML Policies
NASA & Intelesense Technologies
Worldwide Geospatial Data Collaboration
by Dr. Kevin Montgomery and his team
CEO, Intelesense Technologies, Inc.
Sr. Researcher, Stanford University

As we look to the future, humankind faces
challenges that are increasing, while our resources are ever
dwindling. To survive and thrive we need to work together- no one
individual or organization, agency or even government can address
these global challenges all by themselves. As we look across many
groups in government, academia, and industry, we see similar trends
and needs emerge- the need to access and integrate many types of
multimodal data from many sources, the need to collaborate with
others both inside and outside our own organizations irrespective of
geographic location, and the desire to develop a shared
understanding, better decision-making, and to coordinate action.
What if we could integrate our data and leverage our shared
resources? What if we could harness our shared knowledge and
enthusiasm? What if together we could be much more than we could be
alone? How would the world be impacted if such a shared, global
collaboration and geospatial infrastructure were available?
Read more on Collaborate.org to be Showcased in Fourth Annual COM.Geo Conference (COM.Geo 2013)
Collaborate.org is an open global online community of people, working together and sharing resources, expertise and enthusiasm, empowered with advanced technologies like collaboration and visualization tools, and all the world’s geospatial data at your fingertips- including real-time sensor data, GIS and database information, news/RSS and social media, and satellite and aerial imagery. It currently hosts over 2.2M layers, estimated at over 5PB of data, with the easy ability for users to upload and share their own data with those they wish. It’s Very Big Data leveraging a worldwide cloud computing infrastructure, with crowdsourced data acquisition and quality, and advanced visualization and collaboration tools- everything people need to work together in one place to empower them to do Great Things.
Location Based Access Control on Geospatial Data with GeoXACML Policies
by Dr. Andreas Matheus
Elected member of the OGC Architecture Board
Member of OGC Technical Committee
Editor of OGC Draft Implementation Specification “OpenGIS Geospatial eXtensible Access Control Markup Language (GeoXACML)”


Introduction
Many different types of high quality and up-to-date geospatial information are available from different providers. Often, Intranet solutions exist where trusted users can access information with very few access constraints. In contrast, making information available to users outside of a trusted environment requires the implementation of many security requirements of which Access Control is paramount.
Challenge
When implementing access control systems, a challenge exists in enabling access rights that are highly dependent on many different things. Therefore, it is usually a good idea to separate the implementation and the configuration of the access control system. This allows the use of mature software that can be configured to enforce specific access rights.
About the Workshop
This workshop is divided in two parts:
1. The theoretical base of the GeoXACML Policy Language:
GeoXACML is the OGC standard language aimed specifically at declaring and enforcing geo-specific access rights, which protect access to geospatial data or services. This workshop will introduce GeoXACML and will illustrate how to write GeoXACML Policies for OGC WMS and WFS services.
2. The practical portion of the workshop will provide attendees an environment for hands-on exercises to experiment writing GeoXACML policies and testing them in a demo environment.
Workshop Agenda
09:00 – 09:15 Speaker and
audience intro
09:15 – 10:00 Brief introduction to security
requirements and standards including GeoXACML
10:00 – 10:15 “Cross Border” Use – Full system
integration demo focusing on Access Control
10:15 – 11:15 Hands-On session
11:15 – 11:45 Use Case “Fire at the airport”
walk-through
11:45 – 12:00 Wrap-up
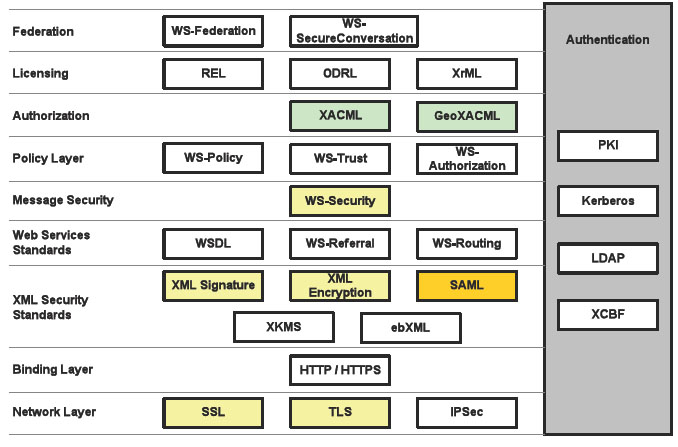
Brief introduction to security requirements and standards
Requirements are
• Authentication
• Access Control
• Integrity
• Confidentiality
• Availability
• Authenticity
• (Non-Repudiation)
Available standards for implementing the requirements:
More workshops will be released soon.